本文为看雪论坛优秀文章
看雪论坛作者ID:Imyang
1
简述流程
2
前期准备
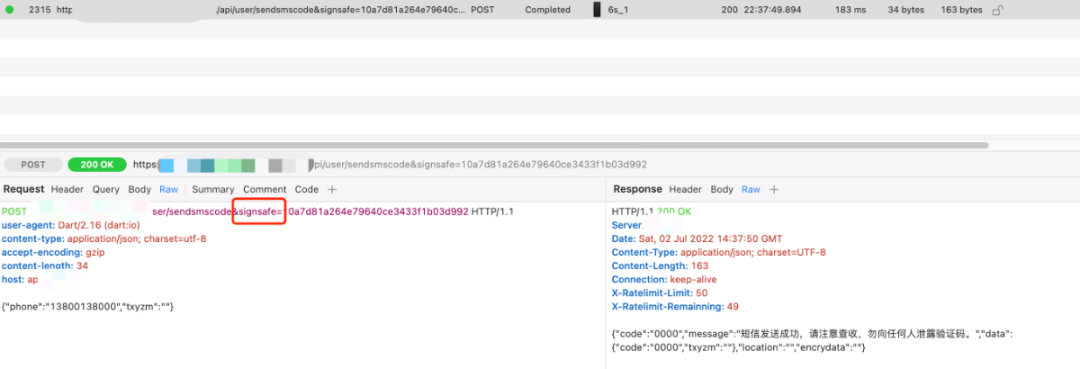
2.1 抓包,确定需要分析的signsafe算法。
2.2 frida-ios-dump砸壳
2.3 reFlutter重打包
2.4 ios-app-signer 重签名
2.5 xcode安装重打包的ipa
2.6 查看dump.dart日志
2.7 ida加载App.framework下的App文件
3
signsafe详细分析流程
Library:'package:pointycastle/digests/md5.dart' Class: MD5Digest extends MD4FamilyDigest implements Type: Digest {FactoryConfig factoryConfig = sentinel ;Function 'get:algorithmName': getter const. String: null {Code Offset: _kDartIsolateSnapshotInstructions + 0x0000000000cc8a1c}Function 'get:digestSize': getter const. String: null {Code Offset: _kDartIsolateSnapshotInstructions + 0x0000000000ccd5f4}Function 'MD5Digest.': constructor. String: null {Code Offset: _kDartIsolateSnapshotInstructions + 0x0000000000002828}Function 'resetState':. String: null {Code Offset: _kDartIsolateSnapshotInstructions + 0x0000000000cc4d98}Function 'processBlock':. String: null {Code Offset: _kDartIsolateSnapshotInstructions + 0x0000000000ce4ea0}}
Library:'package:crypto/src/md5.dart' Class: [email protected] extends HashSink {Function '[email protected]': constructor. String: null {Code Offset: _kDartIsolateSnapshotInstructions + 0x000000000026309c}Function 'updateHash':. String: null {Code Offset: _kDartIsolateSnapshotInstructions + 0x0000000000c649f8}}
Library:'package:crypto/src/md5.dart' Class: [email protected] extends Hash {Function 'startChunkedConversion':. String: null {Code Offset: _kDartIsolateSnapshotInstructions + 0x0000000000c4f2d4}}
function print_native_stack(addr, context) {return ('\r\n[' + addr + '] called from:\n' +Thread.backtrace(context.context, Backtracer.ACCURATE).map(DebugSymbol.fromAddress).join('\n') + '\n');}function hook_md5() {let kDartIsolateSnapshotInstructions = Module.findExportByName("App", "kDartIsolateSnapshotInstructions")console.log(kDartIsolateSnapshotInstructions);let processBlock = kDartIsolateSnapshotInstructions.add(0x0000000000ce4ea0);let updateHash = kDartIsolateSnapshotInstructions.add(0x0000000000c649f8);let startChunkedConversion = kDartIsolateSnapshotInstructions.add(0x0000000000c4f2d4);Interceptor.attach(processBlock, {onEnter(args) {console.log("processBlock:", print_native_stack("processBlock", this));}})Interceptor.attach(updateHash, {onEnter(args) {console.log("updateHash:", print_native_stack("updateHash", this));}})Interceptor.attach(startChunkedConversion, {onEnter(args) {console.log("startChunkedConversion:", print_native_stack("startChunkedConversion", this));}})}
function hook_addr(addr, name) {Interceptor.attach(addr, {onEnter(args) {this.log = []this.log.push(name + " onEnter:\r\n")for(let i = 0; i < 8; i++) {try {this.log.push(hexdump(args[i]), "\r\n");} catch (error) {this.log.push((args[i]), "\r\n");}}}, onLeave(retval) {this.log.push(name + " onLeave:\r\n")try {this.log.push(hexdump(retval), "\r\n");} catch (error) {this.log.push((retval), "\r\n");}this.log.push("=======================")console.log(this.log);}})}function hook_apisign() {let Precompiled_Hmac_Hmac__7814 = DebugSymbol.fromName("Precompiled_Hmac_Hmac__7814")let Precompiled_Hmac_convert_37042 = DebugSymbol.fromName("Precompiled_Hmac_convert_37042")let Precompiled____base64Encode_5267 = DebugSymbol.fromName("Precompiled____base64Encode_5267")let Precompiled_Hash_convert_37041 = DebugSymbol.fromName("Precompiled_Hash_convert_37041")let Precompiled_Digest_toString_34431 = DebugSymbol.fromName("Precompiled_Digest_toString_34431")hook_addr(Precompiled_Hmac_Hmac__7814.address, Precompiled_Hmac_Hmac__7814.name);hook_addr(Precompiled_Hmac_convert_37042.address, Precompiled_Hmac_convert_37042.name);hook_addr(Precompiled____base64Encode_5267.address, Precompiled____base64Encode_5267.name);hook_addr(Precompiled_Hash_convert_37041.address, Precompiled_Hash_convert_37041.name);hook_addr(Precompiled_Digest_toString_34431.address, Precompiled_Digest_toString_34431.name);}
Precompiled_Hmac_Hmac__7814 onEnter:, 0 1 2 3 4 5 6 7 8 9 A B C D E F 0123456789ABCDEF10c0afba9 03 6d 00 00 00 00 00 c0 fb 0a 0c 01 00 00 00 00 .m..............10c0afbb9 00 00 00 14 00 00 00 44 32 33 41 42 43 40 23 35 [email protected]#510c0afbc9 36 00 00 00 00 00 00 00 00 00 00 00 00 00 00 04 6...............。。。。。。Precompiled_Hmac_convert_37042 onEnter:, 0 1 2 3 4 5 6 7 8 9 A B C D E F 0123456789ABCDEF10c0afd79 07 6d 00 00 00 00 00 90 fd 0a 0c 01 00 00 00 00 .m..............10c0afd89 00 00 00 9a 00 00 00 61 70 69 2e 78 78 78 2e 63 .......api.xxx.c10c0afd99 6e 2f 78 78 78 78 2f 61 70 69 3f 70 68 6f 6e 65 n/xxxx/api?phone10c0afda9 3d 31 33 38 30 30 31 33 38 30 30 30 26 74 78 79 =13800138000&txy10c0afdb9 7a 6d 3d 26 75 72 69 3d 61 70 69 78 78 78 78 2f zm=&uri=apixxxx/10c0afdc9 61 70 69 2f 75 73 65 72 2f 73 65 6e 64 73 6d 73 api/user/sendsms10c0afdd9 63 6f 64 65 00 00 00 00 00 00 00 00 00 00 00 04 code............。。。。。。Precompiled____base64Encode_5267 onEnter:, 0 1 2 3 4 5 6 7 8 9 A B C D E F 0123456789ABCDEF10c0b0789 03 6d 00 00 00 00 00 a0 07 0b 0c 01 00 00 00 00 .m..............10c0b0799 00 00 00 28 00 00 00 f6 41 84 fc 8b 76 4a f3 03 ...(....A...vJ..10c0b07a9 a0 fe d9 2f e8 5d 85 0f ee 6d b2 00 00 00 00 04 .../.]...m......。。。。。。,Precompiled____base64Encode_5267 onLeave:, 0 1 2 3 4 5 6 7 8 9 A B C D E F 0123456789ABCDEF10c0b0859 03 55 00 00 00 00 00 38 00 00 00 00 00 00 00 39 .U.....8.......910c0b0869 6b 47 45 2f 49 74 32 53 76 4d 44 6f 50 37 5a 4c kGE/It2SvMDoP7ZL10c0b0879 2b 68 64 68 51 2f 75 62 62 49 3d 00 00 00 00 00 +hdhQ/ubbI=.....。。。。。。,Precompiled_Digest_toString_34431 onLeave:, 0 1 2 3 4 5 6 7 8 9 A B C D E F 0123456789ABCDEF10c0b0d19 03 55 00 00 00 00 00 40 00 00 00 00 00 00 00 31 [email protected]10c0b0d29 30 61 37 64 38 31 61 32 36 34 65 37 39 36 34 30 0a7d81a264e7964010c0b0d39 63 65 33 34 33 33 66 31 62 30 33 64 39 39 32 00 ce3433f1b03d992.
md5("9kGE/It2SvMDoP7ZL+hdhQ/ubbI=") -> 10a7d81a264e79640ce3433f1b03d99200000000 f6 41 84 fc 8b 76 4a f3 03 a0 fe d9 2f e8 5d 85 |öA.ü.vJó. þÙ/è].|00000010 0f ee 6d b2 |.îm²|进行 base64 可以得到9kGE/It2SvMDoP7ZL+hdhQ/ubbI=
hmac_sha1("[email protected]#56", "api.xxx.cn/xxxx/api?phone=13800138000&txyzm=&uri=apixxxx/api/user/sendsmscode") //已打码xxxx4
总结
参考工具:
看雪ID:Imyang
https://bbs.pediy.com/user-home-548459.htm
# 往期推荐
球分享
球点赞
球在看
点击“阅读原文”,了解更多!
文章来源: http://mp.weixin.qq.com/s?__biz=MjM5NTc2MDYxMw==&mid=2458458802&idx=1&sn=d2b5e89ad8a819c164d9cdfaa7fa8353&chksm=b18e2a3886f9a32e6b4547aa7286c2e69895a3695d092f63995db0d1d4c498332acb7a8565a2#rd
如有侵权请联系:admin#unsafe.sh
如有侵权请联系:admin#unsafe.sh