Microsoft has fixed 84 vulnerabilities (aka flaws) in the July 2022 update, including four (4) vulnerabilities classified as Critical as they allow Remote Code Execution (RCE). This month’s Patch Tuesday cumulative Windows update includes the fix for one (1) actively exploited zero-day vulnerability (CVE-2022-22047). Earlier this month, July 6, 2022, Microsoft also released two (2) Microsoft Edge (Chromium-Based) security updates as well.
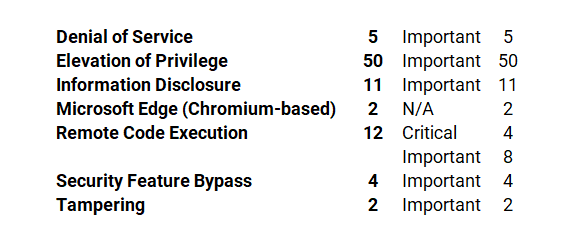
Microsoft has fixed several flaws in its software, including Denial of Service (DoS), Elevation of Privilege, Information Disclosure, Microsoft Edge (Chromium-based), Remote Code Execution (RCE), Security Feature Bypass, and Tampering.
Many of the vulnerabilities patched this month relate to remote code execution, but there are no reports of active exploitation (in the wild) except for CVE-2022-22047, a Windows CSRSS Elevation of Privilege Vulnerability.
The July 2022 Microsoft vulnerabilities are classified as follows:

Notable Microsoft Vulnerabilities Patched
CVE-2022-22047 | Windows CSRSS Elevation of Privilege Vulnerability
This vulnerability has a CVSSv3.1 score of 7.8/10.
Elevation of Privilege – Important – An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. (Article 5015874)
Exploitability Assessment: Exploitation Detected
This month’s advisory covers multiple Microsoft product families, including Azure, Browser, ESU, Microsoft Dynamics, Microsoft Office, System Center, and Windows.
A total of 63 unique Microsoft products/versions are affected.
Downloads include Monthly Rollup, Security Only, and Security Updates.
CVE-2022-30221 | Windows Graphics Component Remote Code Execution Vulnerability
This vulnerability has a CVSSv3.1 score of 8.8/10.
An attacker would have to convince a targeted user to connect to a malicious RDP server. Upon connecting, the malicious server could execute code on the victim’s system in the context of the targeted user.
Windows 7 Service Pack 1 or Windows Server 2008 R2 Service Pack 1 are only affected by this vulnerability if either RDP 8.0 or RDP 8.1 is installed. If you do not have either of these versions of RDP installed on Windows 7 SP1 or Window Server 2008 R2 SP1, then you are not affected by this vulnerability.
Exploitability Assessment: Exploitation Less Likely
CVE-2022-22029 | Windows Network File System Remote Code Execution Vulnerability
This vulnerability has a CVSSv3.1 score of 8.1/10.
This vulnerability could be exploited over the network by making an unauthenticated, specially crafted call to a Network File System (NFS) service to trigger a Remote Code Execution (RCE).
Successful exploitation of this vulnerability requires an attacker to invest time in repeated exploitation attempts through sending constant or intermittent data.
Exploitability Assessment: Exploitation Less Likely
CVE-2022-22038 | Remote Procedure Call Runtime Remote Code Execution Vulnerability
This vulnerability has a CVSSv3.1 score of 8.1/10.
Successful exploitation of this vulnerability requires an attacker to invest time in repeated exploitation attempts through sending constant or intermittent data.
Exploitability Assessment: Exploitation Less Likely
CVE-2022-22039 | Windows Network File System Remote Code Execution Vulnerability
This vulnerability has a CVSSv3.1 score of 7.5/10.
Successful exploitation of this vulnerability requires an attacker to win a race condition.
This vulnerability could be exploited over the network by making an unauthenticated, specially crafted call to a Network File System (NFS) service to trigger a Remote Code Execution (RCE).
Exploitability Assessment: Exploitation Less Likely
Microsoft Last But Not Least
Earlier in July, Microsoft released Microsoft Edge (Chromium-based) vulnerabilities CVE-2022-2294 and CVE-2022-2295. The vulnerability assigned to each of these CVEs is in the Chromium Open Source Software (OSS) which is consumed by Microsoft Edge. It is being documented in the Security Update Guide to announce that the latest version of Microsoft Edge (Chromium-based) is no longer vulnerable. Please see Security Update Guide Supports CVEs Assigned by Industry Partners for more information.