SEC Consult SA-20250923-0 :: Missing Certificate Validation leading to RCE in CleverControl employee monitoring software #CVE-2025-10548
CleverControl员工监控软件存在高危漏洞(CVE-2025-10548),因缺少证书验证导致远程代码执行。攻击者可利用中间人攻击替换下载文件并以系统权限执行恶意代码。厂商未提供补丁,建议用户联系厂商并进行安全审查。 2025-9-25 22:49:43 Author: seclists.org(查看原文) 阅读量:4 收藏
CleverControl员工监控软件存在高危漏洞(CVE-2025-10548),因缺少证书验证导致远程代码执行。攻击者可利用中间人攻击替换下载文件并以系统权限执行恶意代码。厂商未提供补丁,建议用户联系厂商并进行安全审查。 2025-9-25 22:49:43 Author: seclists.org(查看原文) 阅读量:4 收藏

Full Disclosure mailing list archives
From: SEC Consult Vulnerability Lab via Fulldisclosure <fulldisclosure () seclists org>
Date: Tue, 23 Sep 2025 07:58:36 +0000
SEC Consult Vulnerability Lab Security Advisory < 20250923-0 >
=======================================================================
title: Missing Certificate Validation leading to RCE
product: CleverControl employee monitoring software
vulnerable version: 11.5.1041.6
fixed version: -
CVE number: CVE-2025-10548
impact: high
homepage: https://clevercontrol.com
found: 2025-05-23
by: Daniel Hirschberger (Office Bochum)
Thorger Jansen (Office Bochum)
Tobias Niemann (Office Bochum)
Marius Renner (Office Bochum)
SEC Consult Vulnerability Lab
An integrated part of SEC Consult, an Eviden business
Europe | Asia
https://www.sec-consult.com
=======================================================================
Vendor description:
-------------------
"Imagine a work environment where employee monitoring software empowers, not
restricts. Where collaborative insights fuel optimizations and breakthroughs,
and employee well-being stands hand-in-hand with shared success. This is the
environment CleverControl brings to life. We're not about micromanagement. We're
about unlocking team potential through powerful, ethical tools. Our employee
monitoring software sheds light on workflow patterns, revealing trends,
bottlenecks, and hidden growth opportunities, all while ensuring ironclad data
security and encryption (in compliance with ISO 27001 Standard and stored on
secure servers) and ethical usage policy."
Source: https://clevercontrol.com/
Business recommendation:
------------------------
The vendor was unresponsive and did not answer to our communication attempts.
Therefore, a patch is not available for this security issue. End users of this
product should contact the vendor and demand a patch.
SEC Consult highly recommends performing a thorough security review of the product
conducted by security professionals to identify and resolve potential further
security issues.
Vulnerability overview/description:
-----------------------------------
1) Missing Certificate Validation leading to RCE (CVE-2025-10548)
When deploying the CleverControl MSI, two executables are downloaded without
checking the validity of the server certificate. Those are then executed with
SYSTEM rights. This enables an adversary-in-the-middle attacker to gain code
execution with elevated privileges on the system.
Proof of concept:
-----------------
1) Missing Certificate Validation leading to RCE (CVE-2025-10548)
When the MSI installer file is opened with 7-zip, two script files,
`instredist.cmd` and `srec.cmd` are revealed.
<scripts.png>
Contents of `instredist.cmd`:
--------------------------------------------------------------------------------
curl.exe --insecure -o c:\ProgramData\{FO16FA1A-AA91-C56A-654F-E3865DA10DAT}\vc_redist.x86.exe
https://cdn.cdndownload.net/vc/vc_redist.x86.exe
c:\ProgramData\{FO16FA1A-AA91-C56A-654F-E3865DA10DAT}\vc_redist.x86.exe /install /quiet /norestart /log redist.log
--------------------------------------------------------------------------------
Contents of `srec.cmd`:
--------------------------------------------------------------------------------
curl.exe --insecure -o "C:\ProgramData\{FO16FA1A-AA91-C56A-654F-E3865DA10DAT}\srec(%1).msi"
https://cdn.cdndownload.net/sprec/%2/srec(%1).msi
msiexec /x "C:\ProgramData\{FO16FA1A-AA91-C56A-654F-E3865DA10DAT}\srec(%1).msi" /qn
msiexec /i "C:\ProgramData\{FO16FA1A-AA91-C56A-654F-E3865DA10DAT}\srec(%1).msi" /qn
--------------------------------------------------------------------------------
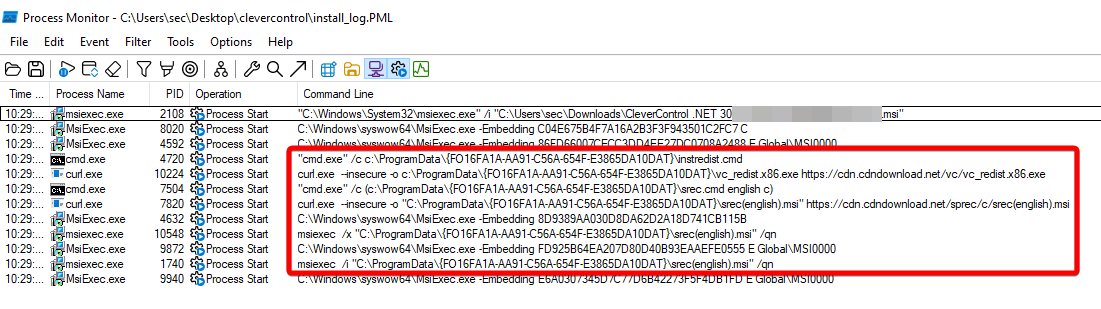
Monitoring the installation process with `ProcMon` shows that these scripts are
indeed executed during the installation:
<procmon.png>
Because curl.exe is started with the `--insecure` flag, the TLS certificate of
the server is not validated. This means that the TLS connection can be
intercepted by an attacker with an adversary-in-the-middle attack.
Therefore, an attacker who can perform such an attack can respond with malicious
files like `vc_redist.x86.exe` or `srec(english).msi` and execute malware with
SYSTEM privileges.
This attack is demonstrated in the following animation which mimics an
adversary-in-the-middle attacker by hard-coding the DNS resolution for
`cdn.cdndownload.net` to point to localhost and by hosting the malicious file
on localhost with `updog`. The malicious .exe file was generated with the following
msfvenom command:
--------------------------------------------------------------------------------
msfvenom -p windows/adduser USER=owned -f exe -o vc_redist.x86.exe
--------------------------------------------------------------------------------
<clevercontrol.webm>
Vulnerable / tested versions:
-----------------------------
The following version has been tested which was the latest version available
at the time of the test:
* 11.5.1041.6
It is assumed that previous versions are affected as well.
Vendor contact timeline:
------------------------
2025-07-02: Contacting vendor through support () clevercontrol com; No response
2025-07-21: Asking vendor if they received our initial email. No response
2025-09-16: Sending publication deadline of 23rd September to vendor via email.
No response.
2025-09-23: Release of security advisory.
Solution:
---------
The vendor was unresponsive and did not answer to our communication attempts.
Therefore, a patch is not available for this security issue. End users of this
product should contact the vendor and demand a patch.
Workaround:
-----------
None
Advisory URL:
-------------
https://sec-consult.com/vulnerability-lab/
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
SEC Consult Vulnerability Lab
An integrated part of SEC Consult, an Eviden business
Europe | Asia
About SEC Consult Vulnerability Lab
The SEC Consult Vulnerability Lab is an integrated part of SEC Consult, an
Eviden business. It ensures the continued knowledge gain of SEC Consult in the
field of network and application security to stay ahead of the attacker. The
SEC Consult Vulnerability Lab supports high-quality penetration testing and
the evaluation of new offensive and defensive technologies for our customers.
Hence our customers obtain the most current information about vulnerabilities
and valid recommendation about the risk profile of new technologies.
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
Interested to work with the experts of SEC Consult?
Send us your application https://sec-consult.com/career/
Interested in improving your cyber security with the experts of SEC Consult?
Contact our local offices https://sec-consult.com/contact/
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
Mail: security-research at sec-consult dot com
Web: https://www.sec-consult.com
Blog: https://blog.sec-consult.com
X: https://x.com/sec_consult
EOF Daniel Hirschberger, Thorger Jansen, Tobias Niemann, Marius Renner / @2025
Attachment:
clevercontrol.webm
Description:
Attachment:
smime.p7s
Description: S/MIME Cryptographic Signature
_______________________________________________ Sent through the Full Disclosure mailing list https://nmap.org/mailman/listinfo/fulldisclosure Web Archives & RSS: https://seclists.org/fulldisclosure/
Current thread:
- SEC Consult SA-20250923-0 :: Missing Certificate Validation leading to RCE in CleverControl employee monitoring software #CVE-2025-10548 SEC Consult Vulnerability Lab via Fulldisclosure (Sep 25)
文章来源: https://seclists.org/fulldisclosure/2025/Sep/71
如有侵权请联系:admin#unsafe.sh
如有侵权请联系:admin#unsafe.sh

