2024-6-24 16:50:6 Author: www.tgsoft.it(查看原文) 阅读量:0 收藏
Weekly report by TG Soft's CRAM concerning Italian malspam campaigns.
Below the details of the campaigns massively spread during the week from June 24 to June 30, 2024.
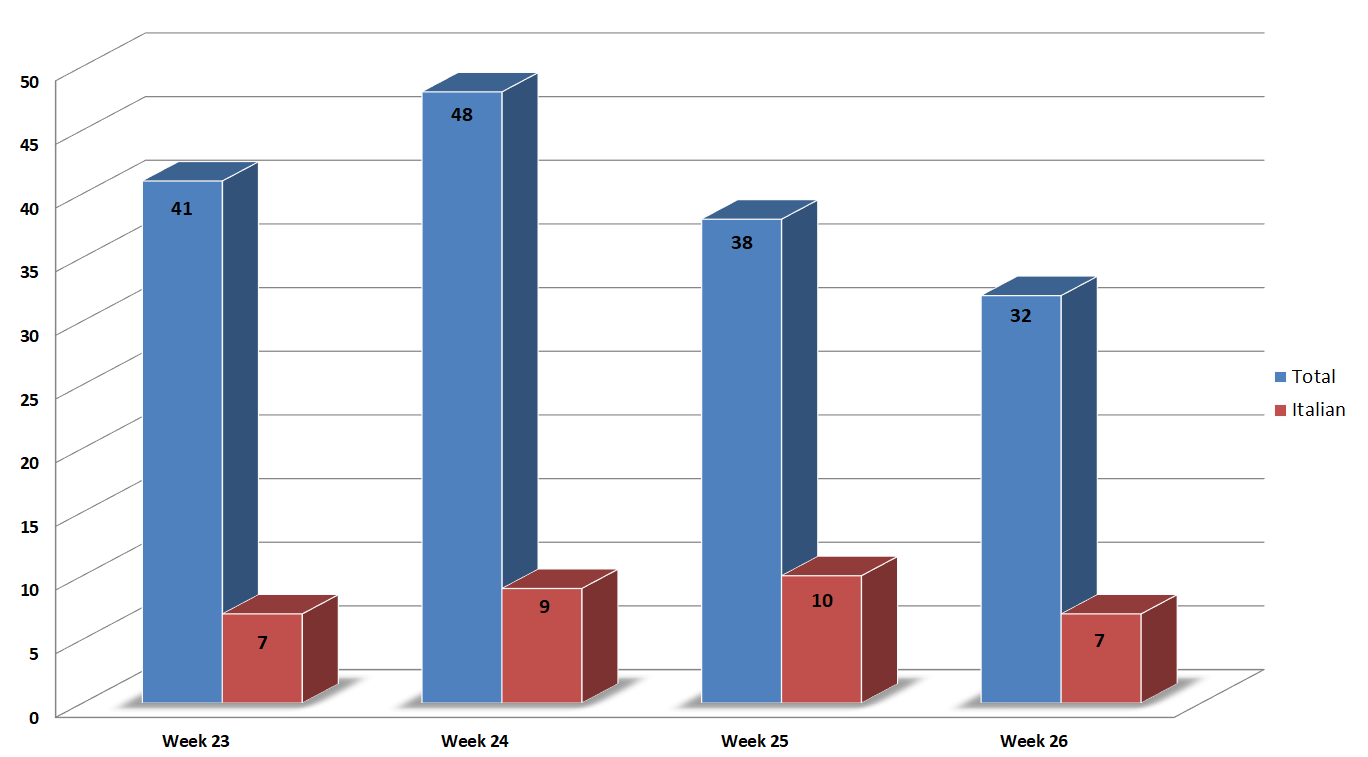
In the monitored week, both global and Italian campaigns decreased compared to the previous week.
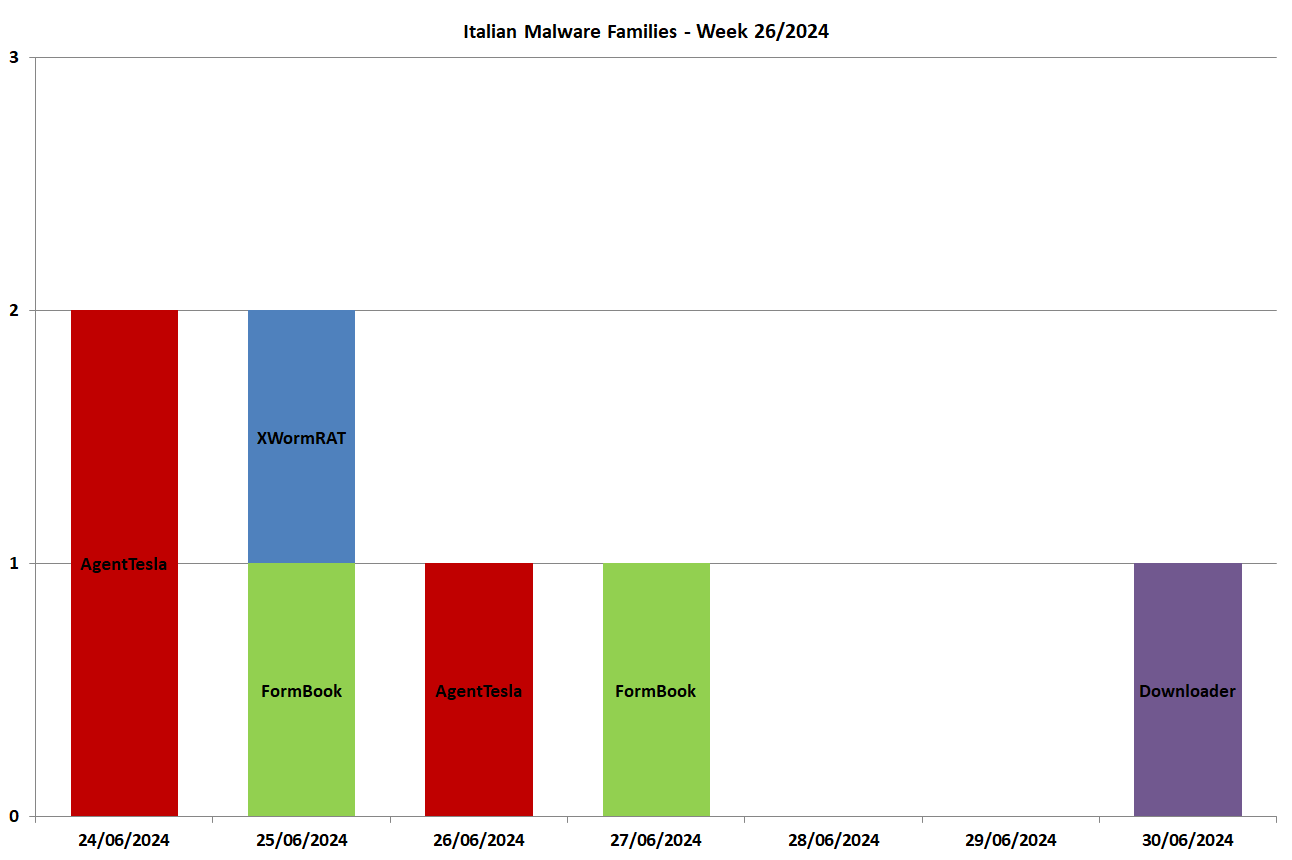
The week was characterized by Password Stealers of the Families: AgentTesla, FormBook and XWorm.
The blue bar indicates the total number of campaigns monitored in Italy in each week, while the red bar concerns campaigns written in Italian (and targeting Italy).
We monitored 32 campaigns during the week, 7 of which used Italian as their language.
In order to understand how the various weeks are divided, below is a small table showing the breakdown of the periods considered:
| Week |
from | to |
| Week_23 | 03/06 | 09/06 |
| Week_24 | 10/06 | 16/06 |
| Week_25 | 17/06 | 23/06 |
| Week_26 | 24/06 | 30/06 |
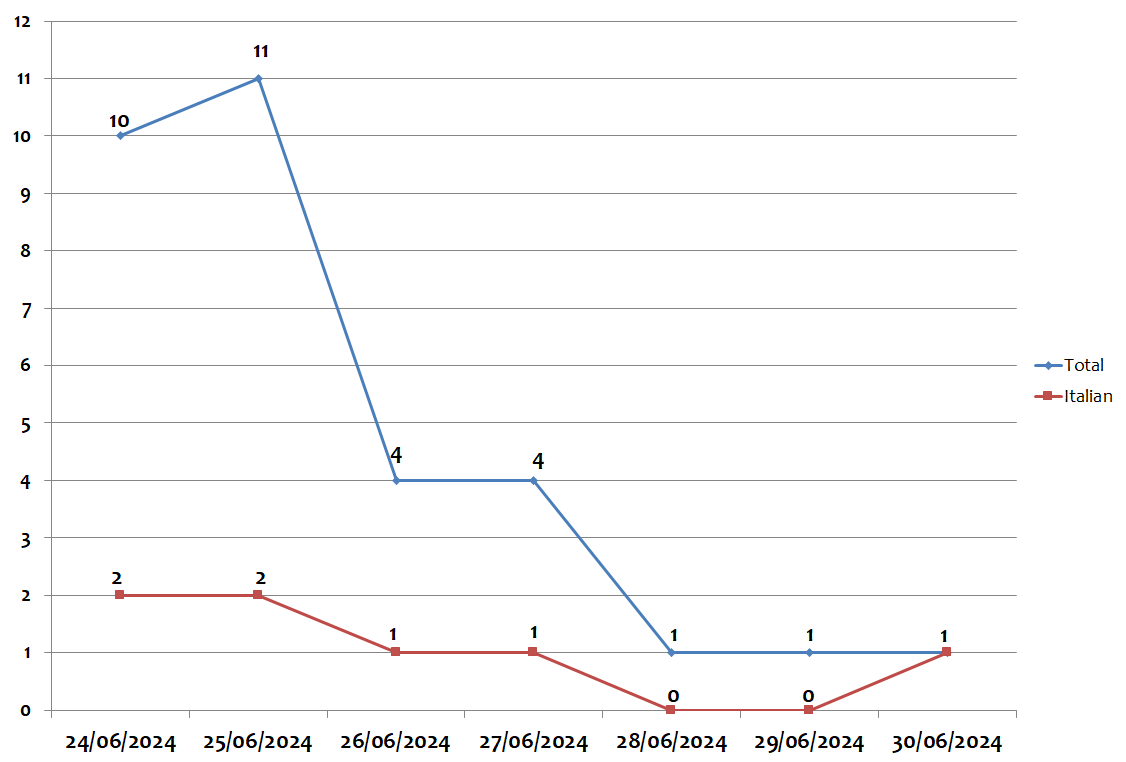
During the week, the peak in global campaigns was found on Tuesday, June 25, with 11 different campaigns per day. The peak of campaigns written in Italian was on Monday 24 and Tuesday 25, June with 2 campaigns for each day, as highlighted by the graph below:
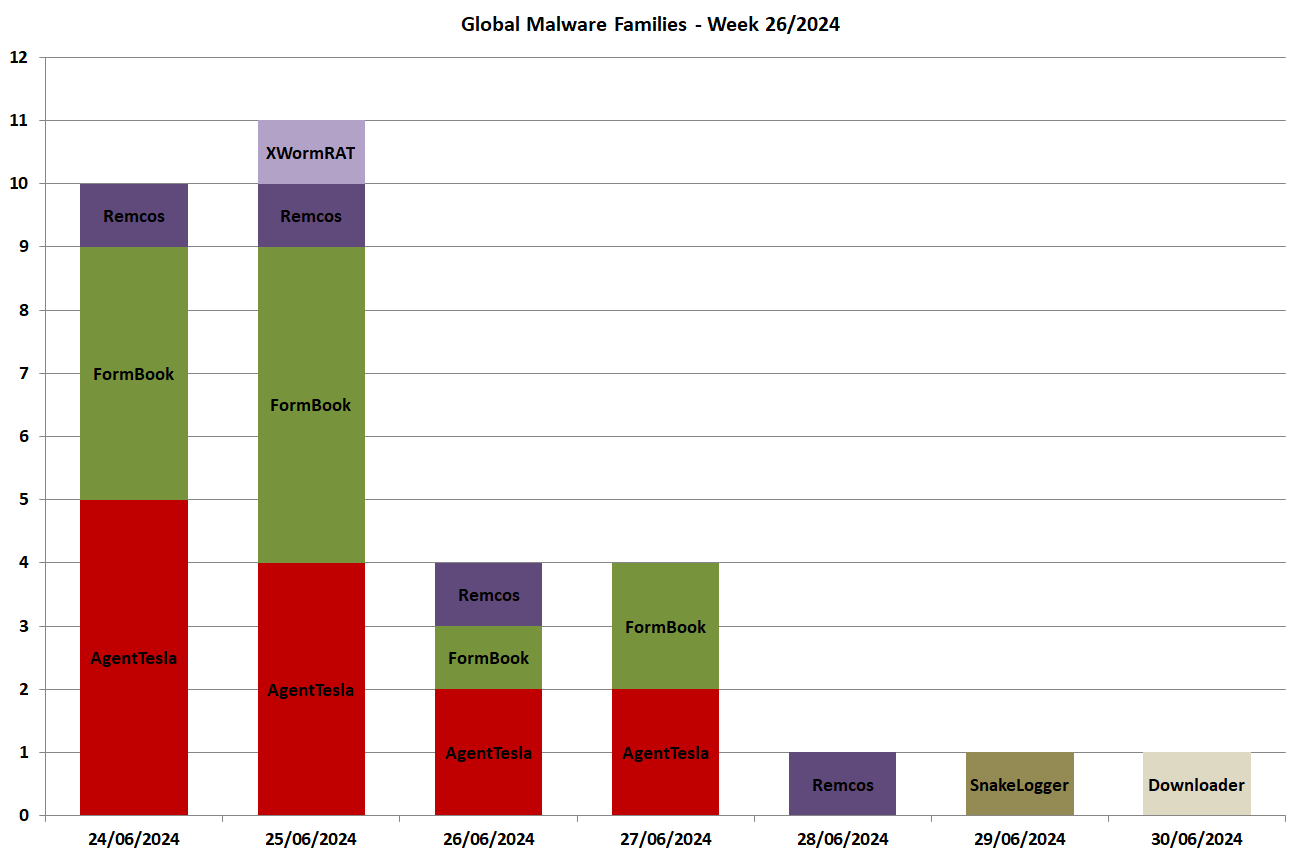
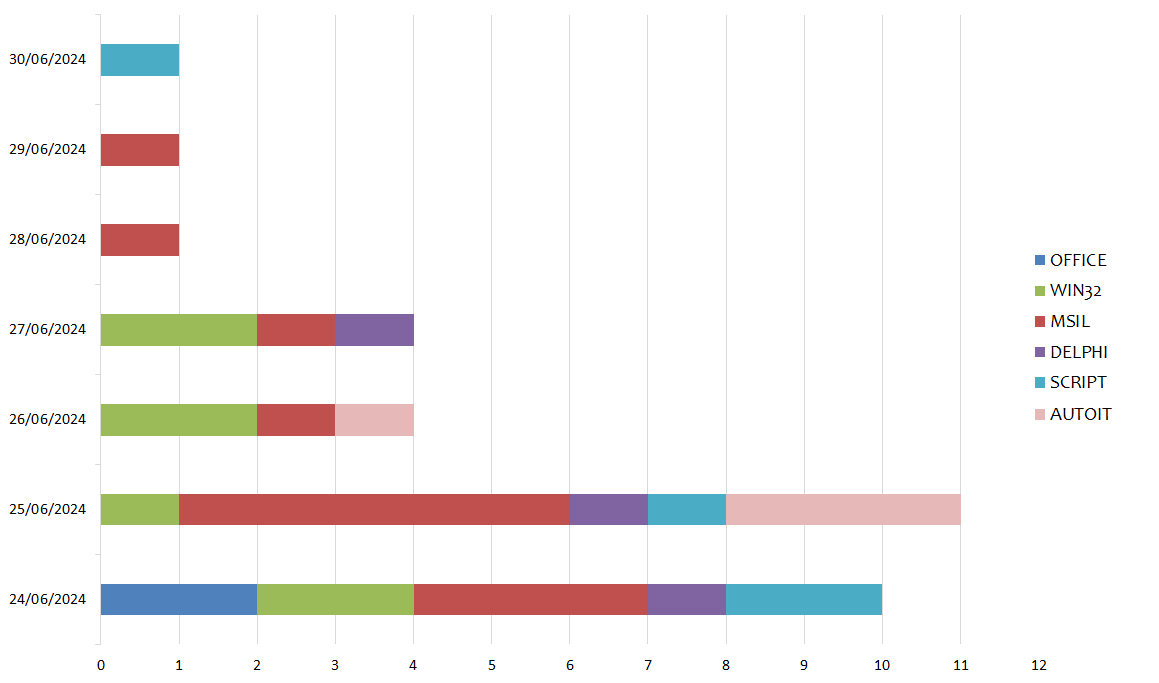
In the following chart we see the malware families spread globally for each day in the week:
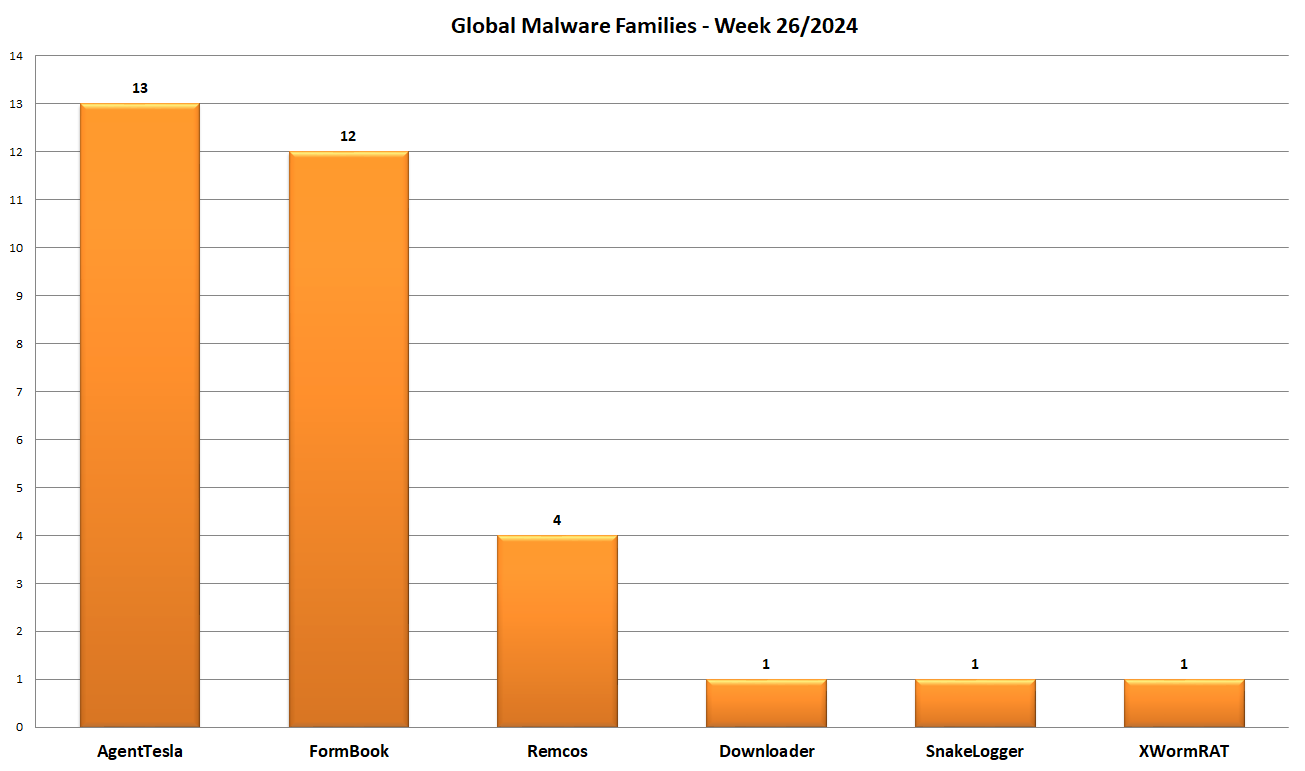
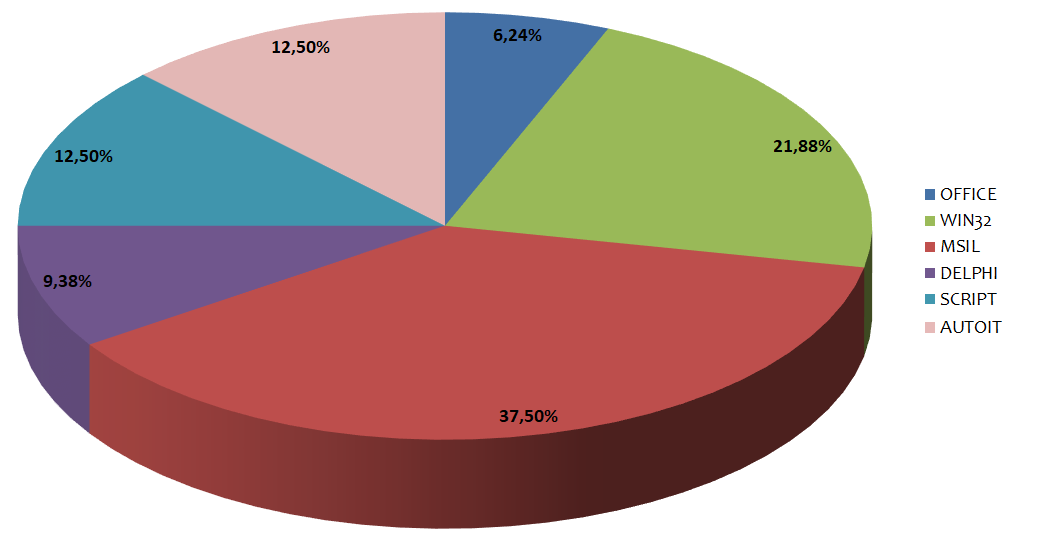
Instead in this graph we see the distribution based on malware family. In the past week 6 different families were detected:
The featured samples this week are MSIL (C#) executibles covering 37.5% of the malware sent via e-mail.
In second place are Win32 executibles with 21.88%.
12.5% of the files are Script (JS, VBS, PS, HTML, Link, etc.).
In the picture below we can see the various types of language used to develop malware:
In the following graph we see the distribution of the various types of languages divided by day:
In this graph we can see the malware families spread during the week with target Italy (written in Italian) and composed of 4 different families:
The Italian campaigns analyzed by TG Soft's C.R.A.M. were grouped according to macro categories, obtained from the subject of the email message used for malware distribution (malspam). Below we see the subjects used in the various campaigns divided by day and type of malware
24/06/2024
AgentTesla - spread through two campaigns, the first themed "Payments" and the second themed "Shipping".
25/06/2024
FormBook - spread through a campaign themed "Invoices".
XWorm - spread through a campaign themed "Others".
26/06/2024
AgentTesla - spread through a campaign themed "Orders".
27/06/2024
FormBook - spread through a campaign themed "Invoices".30/06/2024
Downloader - spread through a campaign themed "Payments".
EMOTET
In the past week the massive sending of MalSpam emails for the spread of the Emotet malware was not detected.
Find out if you are an Emotet target!
TG Soft, as reported in the information "HAVEiBeenEMOTET portal to find out whether a mailbox has been used in malspam campaigns to spread EMOTET ", has provided and maintained for over a year the HAVEiBeenEMOTET service, that can help you to check if your email addresses or domains are targeted by Emotet.
Using this service you can check for free if your email addresses/domains are involved or are targets of MalSpam by Emotet.
Advanced search features and the IOC feed are available by registering and activating the API service at the link: HAVEiBeenEMOTET - API
Check out the May/June campaigns
CRAM
TG Soft's Anti-Malware Research Center
Any information published on our site may be used and published on other websites, blogs, forums, facebook and/or in any other form both in paper and electronic form as long as the source is always and in any case cited explicitly “Source: CRAM by TG Soft www.tgsoft.it” with a clickable link to the original information and / or web page from which textual content, ideas and / or images have been extrapolated.
It will be appreciated in case of use of the information of C.R.A.M. by TG Soft www.tgsoft.it in the report of summary articles the following acknowledgment/thanks “Thanks to Anti-Malware Research Center C.R.A.M. by TG Soft of which we point out the direct link to the original information: [direct clickable link]”
如有侵权请联系:admin#unsafe.sh